- AI-assisted attackers breached Vercel via compromised employee credentials
- Frontend exploits can drain wallets even if smart contracts are secure
- Developers urged to rotate keys and audit access immediately
A new security incident just reminded the entire crypto space of something uncomfortable, the weakest point isn’t always the blockchain itself. Vercel, a major cloud platform powering countless crypto frontends, confirmed a breach after attackers gained access through a compromised employee account tied to a third-party AI tool.

It wasn’t a loud, obvious attack either, more like a quiet entry that escalated quickly. From one compromised account, attackers moved into Google Workspace, then into internal systems, all with what the company described as surprising speed, likely helped by AI tools accelerating the process.
Why This Is a Big Deal for Crypto
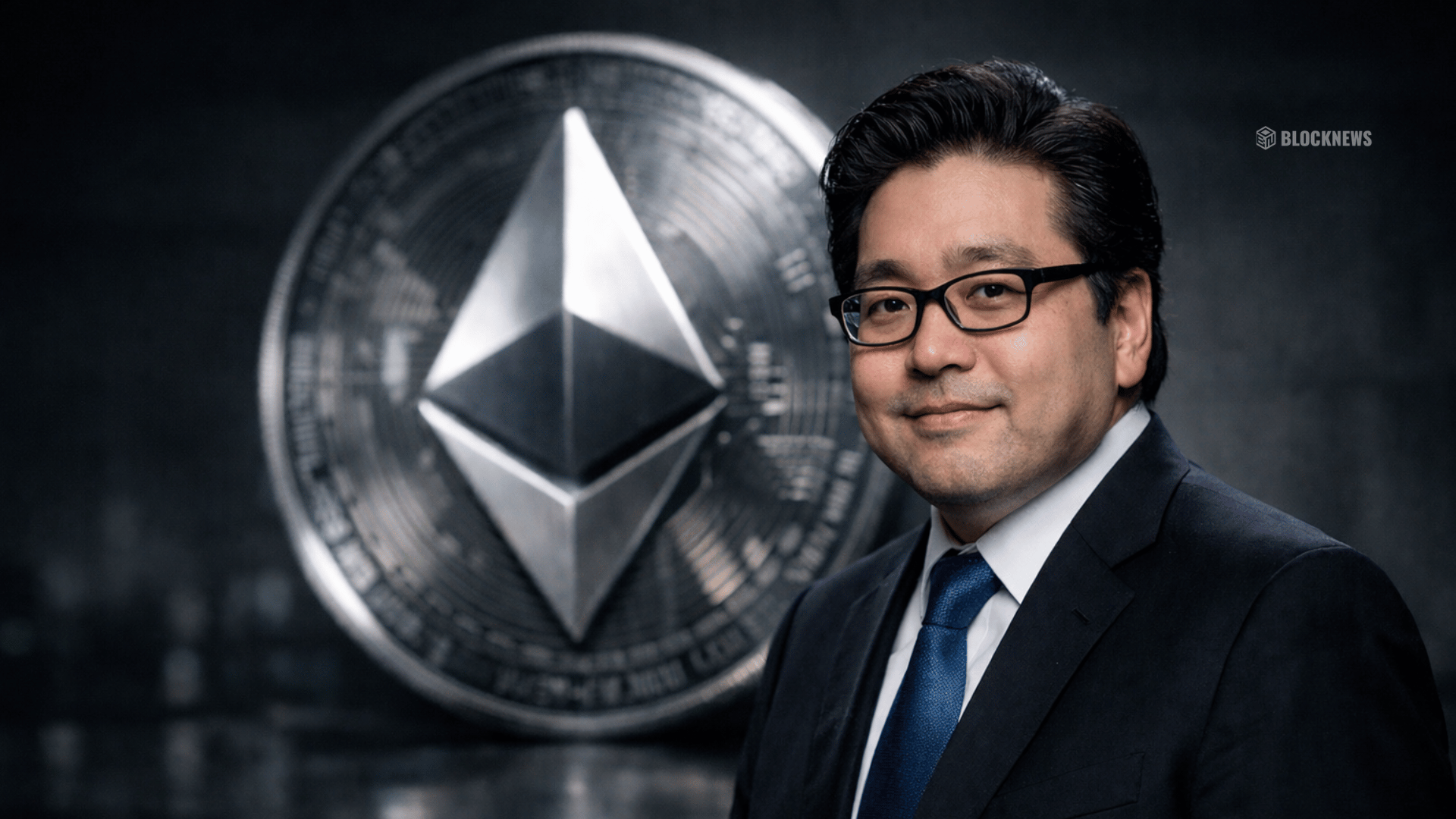
A huge number of DeFi applications rely on frontend infrastructure like Vercel to interact with users. That means even if the smart contracts are perfectly secure, the interface people actually use can become the attack surface.
If that frontend gets compromised, attackers can inject malicious code that tricks users into signing transactions that drain their wallets. And the worst part is, from the user’s perspective, everything looks normal, until it’s not.
We’ve Already Seen This Play Out
This isn’t just a theoretical risk, it’s already happened. The recent CoW Swap incident saw a user lose over $300,000, not because the protocol failed, but because the frontend was compromised.
That’s the scenario developers worry about most, everything working as intended on-chain, while the layer users trust quietly betrays them. It’s subtle, and that makes it dangerous.
Experts Are Raising Red Flags
Security researchers are warning that phrases like “limited impact” don’t always mean what people think they do. In complex cloud environments, access can spread in ways that aren’t immediately visible, especially when credentials and API keys are involved.

There are also reports suggesting that a known hacking group may be attempting to sell stolen access and data, though that part hasn’t been fully confirmed. Still, it adds another layer of concern around how far this breach could reach.
A Growing Attack Surface in the AI Era
The bigger takeaway here isn’t just about one company or one breach. It’s about how the rapid adoption of AI tools is quietly expanding the attack surface across tech stacks.
Every new integration, every OAuth permission, every external tool connected to internal systems creates another potential entry point. And as attackers get more sophisticated, those small openings become easier to exploit.
What Developers Should Be Doing Now
For developers, the message is pretty clear, act fast. Rotating credentials, auditing access permissions, and reviewing third-party integrations isn’t optional anymore, it’s necessary.
Because in crypto, trust doesn’t just live on-chain. It lives in the interfaces, the tools, and the systems people rely on every day, and right now, those layers are being tested more than ever.
Disclaimer: BlockNews provides independent reporting on crypto, blockchain, and digital finance. All content is for informational purposes only and does not constitute financial advice. Readers should do their own research before making investment decisions. Some articles may use AI tools to assist in drafting, but every piece is reviewed and edited by our editorial team of experienced crypto writers and analysts before publication.

 3 hours ago
17
3 hours ago
17






 English (US) ·
English (US) ·