Blockchain investigator ZachXBT reported that an unknown Kraken user lost $18.2 million in a suspected social engineering scam, with stolen funds already moving across chains.
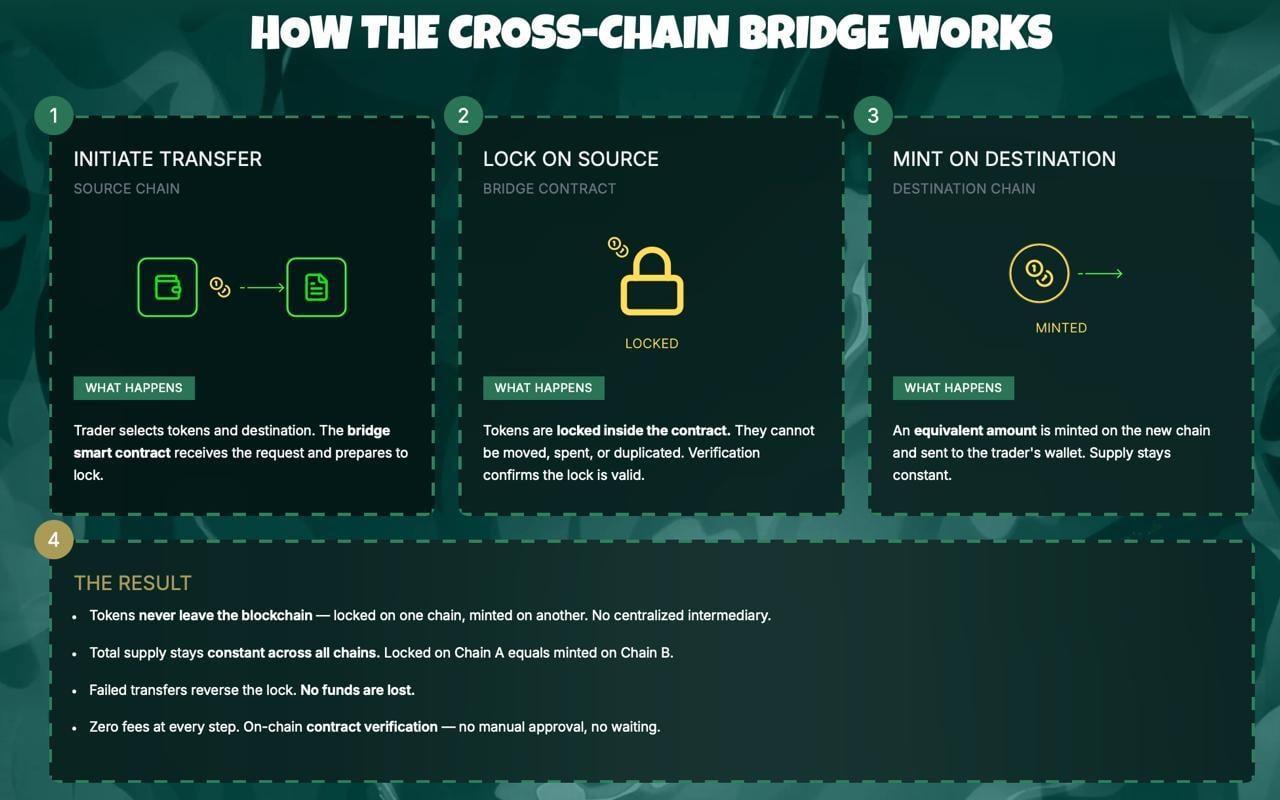
The threat actor began bridging 878 ETH, worth roughly $1.8 million, from Ethereum (ETH) to Bitcoin (BTC) through THORChain using a SafePal wallet. ZachXBT shared the details on his Telegram channel.
Another Social Engineering Victim Funneled Through THORChain
The theft address tied to the incident is 0xC55149BbD560435a9FbEabFdcF9711cf928acA21 on Ethereum, with a corresponding BTC address of 1D8f8956EEFLXN28AHfioEx4ywVbxCz8KN.
On-chain data from the THOR InfoBot confirmed the streaming swap was initiated roughly 45 minutes before the alert went public, adding credence to ZachXBT’s claim.
THORChain, a decentralized cross-chain liquidity protocol, does not require KYC verification. That feature has made it a repeated tool for laundering stolen funds.
In January 2026, an attacker used the same protocol to move portions of $282 million in stolen BTC and Litecoin (LTC) after tricking a hardware wallet user into revealing their seed phrase.
In that case, 818 BTC worth $78 million was swapped into ETH, XRP, and LTC through THORChain.
The blockchain investigator also tracked a $330 million theft in 2025 and a $91 million loss in August of that year, both involving social engineering and cross-chain fund movement.
The 878 ETH visible on-chain may represent only one tranche of the $18.2 million total being moved. Attackers in prior cases frequently split stolen assets across multiple transactions and chains simultaneously.
Neither Kraken nor SafePal has publicly commented on the incident at the time of writing.
The investigation remains in its early stages as on-chain trackers monitor further fund movements from the flagged addresses.
The post Kraken User Allegedly Drained in Suspected Social Engineering Heist appeared first on BeInCrypto.

 1 month ago
37
1 month ago
37






 English (US) ·
English (US) ·