The post Ripple CTO Says RLUSD Evaluation Exposed the Same Risk That Drained $292M From Kelp DAO appeared first on Coinpedia Fintech News
David Schwartz, CTO Emeritus at Ripple, had a pointed observation this week after the Kelp DAO rsETH bridge was exploited for approximately $292 million.
He had seen this coming. Not this specific attack, but the conditions that made it possible.
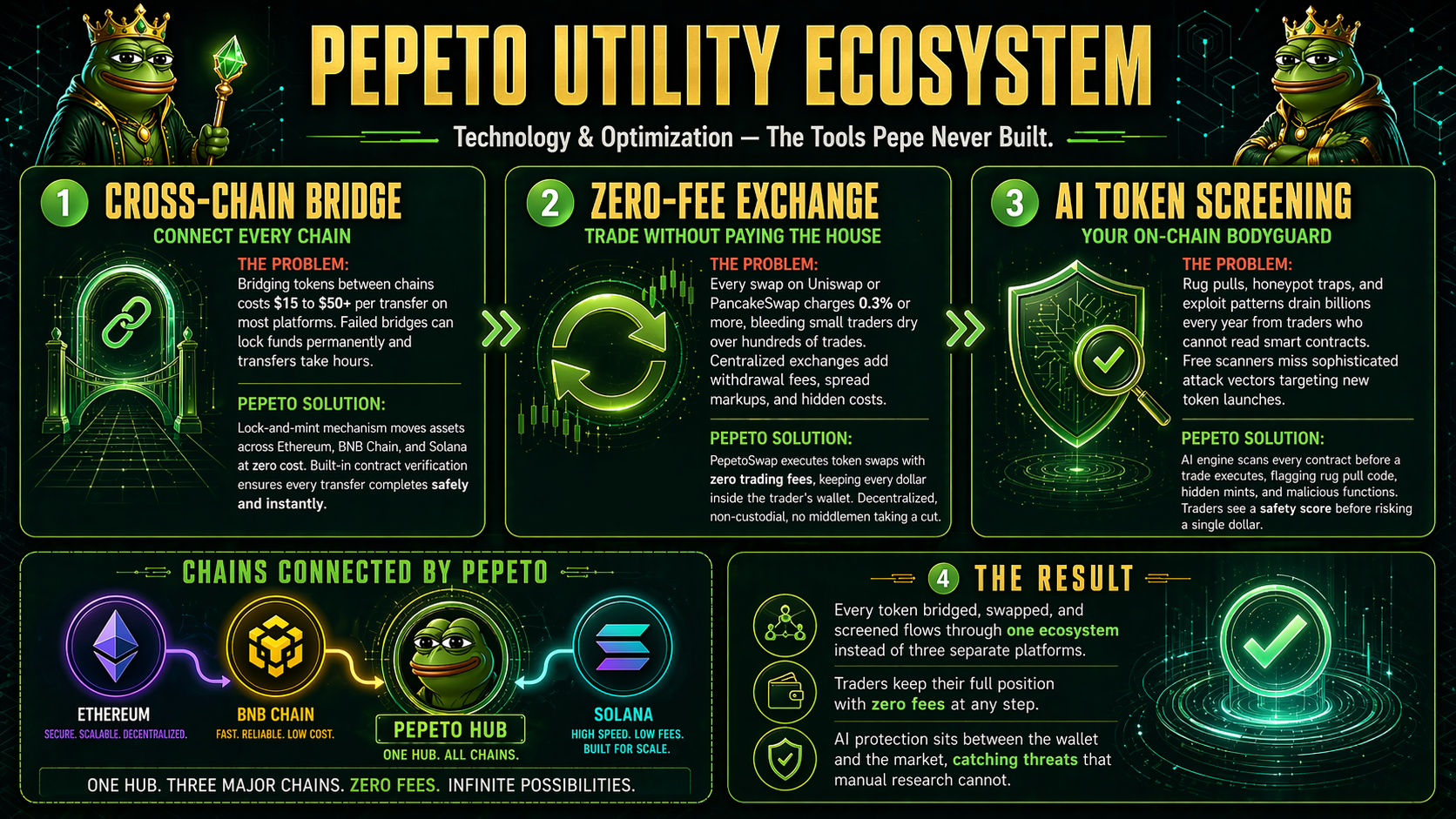
“I evaluated a lot of DeFi bridging systems for use by RLUSD,” Schwartz wrote on X. “I was almost exclusively focused on the security and risk aspect. One thing I noticed is that most schemes were very well designed and had really strong mechanisms available to protect against exactly the type of attack the KelpDAO situation seems to have been caused by.”
The Sales Pitch That Buried the Security Features
What Schwartz described is a pattern he encountered repeatedly during his evaluation process. Bridge providers would pitch their most advanced security features prominently, then almost immediately suggest that those features were optional and that most customers chose not to use them.
“They generally in effect recommended not bothering to use the most important security mechanisms because they have convenience and operational complexity costs,” he wrote. “We were frequently pitched the simplicity and ease of adding more chains with the implicit assumption we wouldn’t bother using the best security features they had.”
“Their sales pitch was that they have the best security features but they’re easy to use and scale, assuming you don’t use the security features,” he said.
What Actually Happened to Kelp DAO
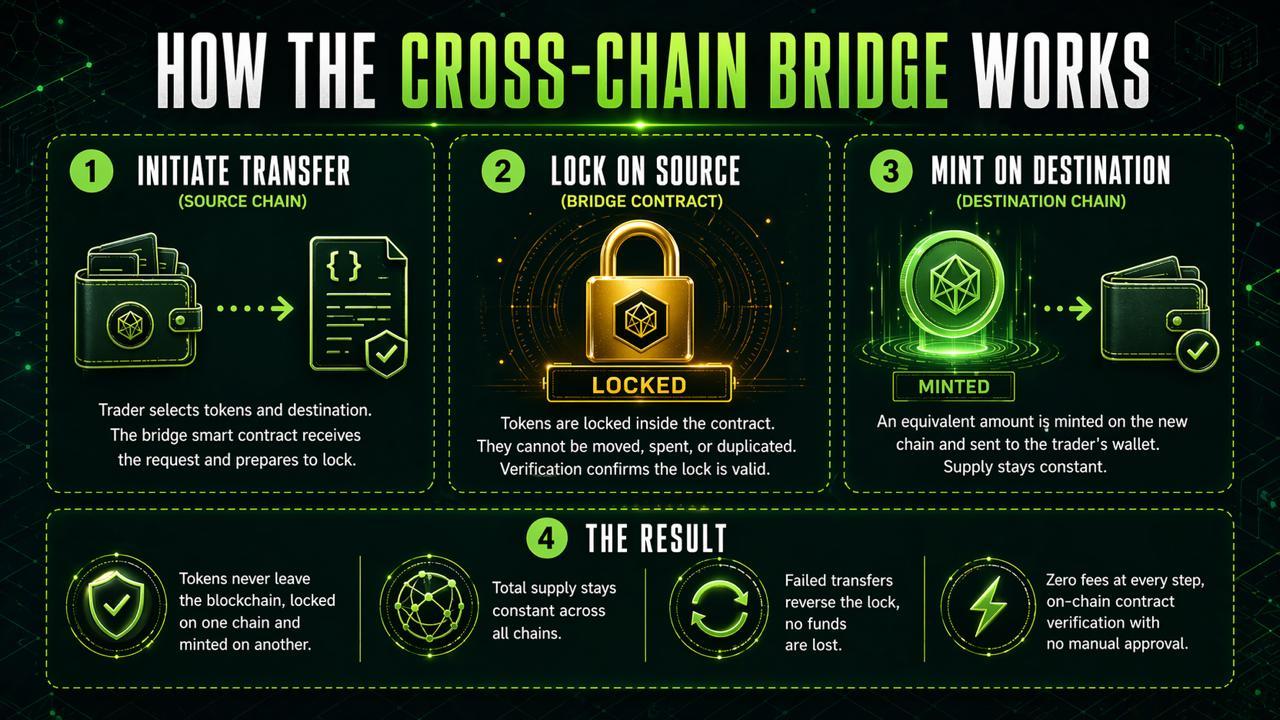
On April 19, Kelp DAO identified suspicious cross-chain activity involving rsETH and paused contracts across mainnet and multiple Layer 2 networks. Approximately 116,500 rsETH was drained through LayerZero-related contract calls, worth around $292 million at current prices.
On-chain analysis from D2 Finance traced the root cause to a private key leak on the source chain, creating a trust issue with OApp nodes that the attacker exploited to manipulate the bridge.
Schwartz offered his own hypothesis about what likely went wrong at the protocol level. “I have a funny feeling part of the problem is going to be something like KelpDAO choosing not to use key LayerZero security features out of convenience,” he wrote.
LayerZero itself offers robust security mechanisms including decentralised verification networks. The question investigators are now examining is whether Kelp DAO configured its implementation using a minimal security setup, specifically a single point of failure with LayerZero Labs as the sole verifier, rather than the more complex but significantly more secure options available.

 2 weeks ago
21
2 weeks ago
21





 English (US) ·
English (US) ·